Stay ahead. Insights and updates from our community
Learn from members of our team and industry-leading experts. Sign up for our weekly newsletter and get key technology insights that keep you ahead of the curve.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.

Announcements
Announcements
All
Show All
The Strategic Case for Qualified Privacy Leadership

Beyond awareness, why professional certifications are the bridge to qualified privacy leadership.
Cybersecurity Training
,
,
March 13, 2026

Perspectives
Vendor Perspectives
All
Show All
Why IAM, IGA, and PAM Break in the Agentic Enterprise

Traditional IAM fails AI agents; identity must shift to governing machine execution and intent.
Identity & Access Management (IAM)
,
,
March 12, 2026

Perspectives
Vendor Perspectives
All
Show All
How AI Is Transforming Third-Party Cyber Risk Management

Manual TPCRM can't scale; AI enables proactive, data-driven risk decisions across the lifecycle.
Risk Management & Compliance
,
,
March 11, 2026

Perspectives
Vendor Perspectives
All
Show All
The Case for Securing the Cloud Workspace Inside and Out

Email security misses interior risk; resilience requires Zero Trust for the cloud workspace.
Email Security
,
,
March 10, 2026

Perspectives
Sage Perspectives
All
Show All
Why Prospects Ask for Your DPO Even When the Law Doesn't

Legal requirements say many don't need a DPO, but prospects still ask. It's now a trust signal.
Data Protection & Privacy
,
,
March 4, 2026

Perspectives
Sage Perspectives
All
Show All
The Hidden Risks of Putting AI in Front of Your Customers

Public-facing AI has unique risks: unclear ownership and skipped monitoring break trust.
Application Security
,
,
February 24, 2026

Perspectives
Sage Perspectives
All
Show All
CVSS Noise to Risk Reduction: Rebuilding Vulnerability Management for Real Impact

Vulnerability scans generate noise. Composite scoring and automation focus on reducible risk.
Vulnerability Management
,
,
February 24, 2026

Perspectives
Vendor Perspectives
All
Show All
The Perimeter Has Moved Closer to the Work

Work happens in browser sessions outside traditional perimeters; security must move to runtime.
Network & Infrastructure Security
,
,
February 23, 2026

Perspectives
Vendor Perspectives
All
Show All
Why Threat-Led Defense Is Reshaping Enterprise Security

Security programs measure controls, not attacker success; threat-led defense tests real procedures.
Threat Detection & Response
,
,
February 17, 2026

Spotlights
Sage Spotlights
All
Show All
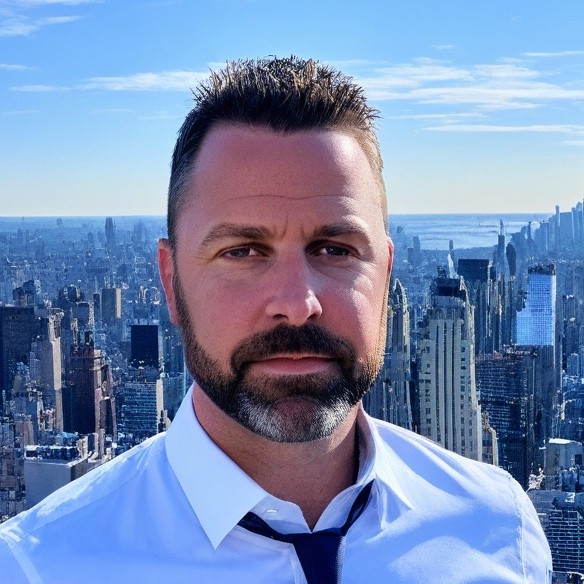
Matthew Marji, Security and Compliance at WorkOS

“Sagetap has made a huge impact on the time to solution. We typically only need to review 2–3 vendors to make a decision, knowing that they’re already a good technical fit for the problem we're trying to solve.”
February 13, 2026

Perspectives
Vendor Perspectives
All
Show All
Why AI-Generated Code Demands a New Application Security Paradigm

AI agents writing code shift AppSec upstream, enabling secure by design with new attack vectors.
Application Security
,
,
February 11, 2026

Perspectives
Vendor Perspectives
All
Show All
Struggling with Human Risk? Take a Page from Adtech

Human error causes 60% of breaches; adtech's behavioral approach offers a better security model.
Cybersecurity Training
,
,
February 5, 2026

Perspectives
Sage Perspectives
All
Show All
Why Identity Fundamentals Matter as Systems Become More Autonomous

AI and automation rely on non-human identities; weak IAM fundamentals expand access gaps.
Identity & Access Management (IAM)
,
,
January 25, 2026

Perspectives
Vendor Perspectives
All
Show All
More Tools, More Tools. How To Avoid Cybersecurity Overload

Security teams face alert fatigue from overlapping tools that don't reduce measurable risk.
Cybersecurity Services
,
,
January 7, 2026

Spotlights
Sage Spotlights
All
Show All
Kenneth Corriveau, CIO at Broughton Partners

"The community that is being built there, the ability to get to another peer and have a conversation — that has really helped out in a few different situations, and it's actually pivoted me from one platform to another."
January 5, 2026

Perspectives
Sage Perspectives
All
Show All
The New Race in Cybersecurity: Your Defense Cycle vs. Their Exploit Cycle

Threat actors weaponize vulnerabilities in hours — defenders must accelerate and assume breach.
Vulnerability Management
,
,
December 8, 2025

Perspectives
Vendor Perspectives
All
Show All
Why DevOps Guardrails Are Becoming Essential for Secure and Scalable Cloud Environments

DevOps guardrails enforce critical security controls without slowing engineering velocity.
Cloud Security
,
,
December 8, 2025

Spotlights
Sage Spotlights
All
Show All
Andy Keller, VP of InfoSec at FiscalNote

"I've discovered well over two dozen vendors to not only potentially replace legacy tools, but also net new functionality — gaps that we have in our security control environment, risky areas of our business operations that these tools address."
December 1, 2025
Spotlights
Sage Spotlights
All
Show All
Matthew Mudry, CISO at Alera Group

"Sagetap just makes everything easy and super simple. Very short and sweet to identify potential solutions, and it doesn't take much time out of your regular day (you can do it at lunch). It also gets you thinking about areas that you may not be focused on currently."
November 3, 2025

Spotlights
Sage Spotlights
All
Show All
Robin Smith, CISO at Great British Energy – Nuclear

"I've never had an engagement on Sagetap that hasn't yielded some decent insights: the very best solutions, the best new ways of working, the best ways of engaging with existing technology solutions. You’re getting the keys to the best minds in cybersecurity."
October 20, 2025

Spotlights
Sage Spotlights
All
Show All
Gareth Hughes, Executive Director, Retail Technology (North America) at The Estée Lauder Companies Inc.

"You get the option to talk to vendors that you may struggle to engage with previously. It’s certainly a different way of going to market and looking for vendors in a traditional way. Sagetap obviously makes the process a lot easier."
October 6, 2025

Spotlights
Sage Spotlights
All
Show All
Sawan Joshi, Global Director of InfoSec at FDM Group

"It's often the startups that bring the innovation the enterprises need, so what I've found amazing about Sagetap is it brings organizations to people building solutions to solve real-world problems. Above everything, it keeps your knowledge strong."
September 15, 2025

Spotlights
Sage Spotlights
All
Show All
Paolo del Mundo, Director of Application Security at The Motley Fool

"We're able to meet with vendors and get the demo that I want without having to go through all the introductions and all the fluff. I don't have to repeat myself n times if I'm talking to n vendors. So it's saved me something like 30% of that entire process."
August 29, 2025

Spotlights
Sage Spotlights
All
Show All
Mick Gomm, Sr. Manager, Vulnerability & Posture Management at Cencora

"As we investigate POCs, that time frame comes around in our budget cycle, we always go to Sagetap to figure out what other vendors we should be looking at and add those to the list. Sagetap has cast a wide net in terms of vendors that they bring in."
August 11, 2025
No articles for this category. Please try another category.
It's Time to Rethink How Enterprise Technology is Bought and Sold
Join the platform where decision-makers and innovators connect to shape the future of enterprise tech.
.svg)








.png)




